My friend Frode Weierud has started adding material in his
site CryptoCellar Tales. Frode
is an expert on WWII crypto history and few people know more on the subject.
Let’s hope that he continues to write about these cases.
Military and intelligence history mostly dealing with World War II.
Tuesday, February 16, 2016
Friday, February 12, 2016
Update on OSS communications from Bern, Switzerland
After going
through my files I’ve discovered more documents that have information on the
compromise of OSS communications in WWII. Thus the following paragraphs are
added in Allen
Dulles and the compromise of OSS codes in WWII:
Report of
Sturmbannführer Huegel
SS-Sturmbannführer
Dr. Klaus Huegel was an important SD official with knowledge of German intelligence
operations in Switzerland and Italy. In CSDIC/CMF/SD
20, he says that when he was working at the SD HQ he saw US intelligence
reports from Bern:
‘A daily bulletin from the German High
Command Cryptographic Service, OKW CHI, was sent to SS Brigadefuehrer
SCHELLENBERG, the Head of Amt VI of the RSHA. It was signed by Generalmajor
THIELE. From Apr 43 till Mar 44, source was in Amt VI, and often saw the
bulletins. He remembers that the following links were intercepted and their traffic
read, translations of matters of interest to Amt VI appearing in the bulletins:
USA Minister HARRISON in BERNE -
WASHINGTON: Three or four signals daily, on the average, were intercepted. All
traffic was read. This enabled Amt VI to judge the Swiss attitude to GERMANY as
seen through American eyes, and also gave a good picture of conditions in
GERMANY. Source says that Mr. HARRISON seemed to be particularly well-informed
on the situation in MUNICH, for instance on the morale of the people and on rifts
between various High Party officials, between GOERING and HIMMLER, RIBBENTROP
and HIMMLER, etc. A conclusion drawn on several occasions in the messages was
that though the population was restive, no organised underground resistance on
a large scale was possible because of the power of the SS and Gestapo and other
security bodies. Source says that Amt VI found these messages of great
interest, and if any points raised required investigation, it was often found
that the information had been correct.’
Under The
Finnish connection:
David Kahn
interviewed some of the Finnish codebreakers in the 1990’s (Aalto, Loimaranta,
Pale) and they clearly remembered US telegrams containing intelligence reports
and information on the German Resistance:
‘Q:
Why did you think the Americans used such weak codes?
A: They had no idea about that, the
question was why the ambassador's telegram, everything in ….. cipher or
ambassador send a list, a long, long telegram about conspiracy against Hitler
with all the names. It was a very, very terrible business,
Another voice: gave them away.
Q: Is that how they caught the
conspirators.’
Wednesday, February 10, 2016
Presentation on solution of historical ciphers
Here is a recent presentation on new methods of solution of
historical cipher systems by mr George Lasry.
Sunday, February 7, 2016
Well that was fast…
One of the
most interesting aspects of Cold War intelligence history is whether the spies
recruited by the Western intelligence agencies (mainly CIA and MI6) were
supplying real information or whether they were double agents. In his recent
article ‘Doubles
Troubles: The CIA and Double Agents during the Cold War’, Benjamin B.
Fischer (former Chief Historian of the Central Intelligence Agency) makes the
case that in Cuba, East Germany and the USSR practically all the CIA agents
were in reality under the control of the enemy security services.
The author
says:
‘During the Cold War the Central Intelligence
Agency (CIA) bucked the law of averages by recruiting double agents on an
industrial scale; it was hoodwinked not a few but many times. The result was a
massive but largely ignored intelligence failure. The facts are available from
official sources.’
I thought
that the article was very interesting and that’s why I linked to it back
in January. The article also mentioned Adolf Tolkachev, the
so called Billion
Dollar Spy. Fischer said:
‘The CIA touts Adolf Tolkachev as its
‘‘billion-dollar spy’’ during the 1980s, asserting that the Soviet electronics
researcher saved the Pentagon several times that amount in research and
development (R&D) and production costs with purloined information on Soviet
military radar and avionics. I believe, however, that Tolkachev was a double
agent, in fact the precursor to the dangles who came after his 1985 arrest………..Tolkachev was not the only double on the CIA’s
payroll. SE Division was handling another agent encrypted EASTBOUND, who also
was selling information on military radars. Soviet and East German sources have
confirmed that the anonymous agent was a double. I believe that Tolkachev and
EASTBOUND were fraternal twins.’
This article which
appeared in a journal with a limited readership seems to have attracted a lot
of attention. The 'great' researchers of the National Security Archive have immediately followed up with the transcripts of a Politburo discussion on Tolkachev.
I don’t know why this organization was so interested in this
case or how they were able to follow up Fischer’s
article so quickly. Since they have such 'superior' investigative skills they
could also look into the compromise of Allied codes and ciphers in WWII. That’s
research that I’d like to see!
Wednesday, February 3, 2016
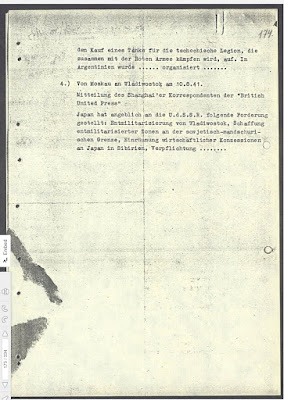
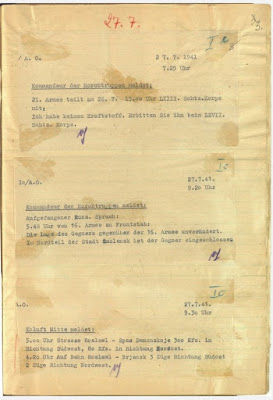
German signals intelligence files in the Russian national archives
At the end of
WWII parts of the German state archives were captured by the Soviet forces and
taken to the Soviet Union. There they were placed in various Soviet state
archives and kept out of reach of researchers. With the fall of the Soviet
Union these archives were opened to researchers but not many people have taken
advantage of that. Thankfully some of these German documents have recently
become available online. The website of The
Russian-German project to digitize German documents in the archives of the
Russian Federation has uploaded a large number of German documents from WWI
and WWII.
The site
says:
‘As a result of the anti-Hitler coalition
victory in the Second World War, documents of Nazi Germany turned up in many
countries, including Russia. Largest collections of German documents are kept
in the Federal archives of the Russian Federation (State Archive of the Russian
Federation (GARF), the Russian State Military Archive (RGVA) and the Russian
State Archive of Socio-Political History (RGASPI)), and in the Central Archive
of the Russian Ministry of Defense (TsAMO). The project to digitize German
documents was initiated by the administration of the Russian President in 2011.
It is executed by the Russian Historical Society, the Ministry of Defense and
the Federal archival agency with support from the German Historical Institute
in Moscow. Coordination committee, overseeing the digitization project, is
headed by S.E. Naryshkin, the Chairman of the State Duma of the Federal
Assembly of the Russian Federation.’
Regarding
German sigint activities during WWII, the search terms ‘Nachrichten Aufklärung’ and ‘horchtruppen’ bring up many
interesting documents. For example:
Baudot
traffic
Reports of
Kommandeur der Horchtruppen Ost
Reports of
Nachrichten Aufklärung Auswertestelle 2
Saturday, January 23, 2016
Interesting articles from academic journals
There are
several journals that deal with military and intelligence history and I try to
follow some of them in case they publish articles that deal with signals
intelligence. Here are some interesting articles from 2015 and early 2016:
Cryptologia
Intelligence
and National Security
International
Journal of Intelligence and CounterIntelligence
Journal of Slavic Military Studies
Sunday, January 10, 2016
Compromise of US cipher teleprinter in 1944
When the
United States entered WWII several cryptosystems were in use by its armed
forces and diplomatic service. The Army and Navy used a small number of SIGABA cipher machines
for their high level traffic and had to rely on a large number of hand systems,
such as the M-138-A
and M-94 strip ciphers and the War
Department Telegraph Code 1919, Military
Intelligence Code, War Department Confidential Code codebooks, for the rest
of the traffic. The State Department relied almost exclusively on hand systems,
specifically the codebooks A1, B1, C1, D1, Gray, Brown and the M-138-A strip
cipher.
In the course
of the war modern cipher machines were designed and built to replace the old
systems and securely cover all types of traffic. In 1942 the M-209 device
was used in the field and in 1943 the cipher teleprinters Converter M-228 - SIGCUM and
SIGTOT were
introduced in communications networks. In the summer of ’43 a new speech
privacy device called SIGSALY became
operational and the first system was used on the link
Pentagon-London. In late 1943 the CCM - Combined
Cipher Machine was used in the Atlantic and in 1944-45 the British
relied on the CCM as much as they did on their own Typex.
By the end of
the war the Americans were using several types of cipher machines, all offering
a high level of security. William Friedman,
head of cipher research at the Army Security Agency, stated in his 1945 reports
that the primary US cipher machines SIGABA and Converter M-228 had proven
completely secure against enemy cryptanalysts.
In the report ‘Security of our high-grade cryptographic systems’, dated March 1945 he said:
‘We come
now to what, in the circumstances, must be considered as the strongest and most
reliable evidence—that which is inferential in and is based upon German
cryptography itself. We know so much about their practices that we can deduce
and assess their cryptographic theories and thus determine the stage of
development they have reached not only in cryptography but also in
cryptanalytics. The overwhelming evidence is that they are far behind us and
have no appreciation of solution techniques which we now regard as commonplace’.
‘To summarize: At the risk of sounding boastful,
it will be stated that the Japanese are not as good as the Germans, and the
latter are not as good as we are in cryptography and especially in
cryptanalysis…… the
conclusion must therefore be clear: They
cannot read and are not reading our high-grade cipher traffic’.
In the report
‘important contributions to communications security, 1939-1945; summary of contributions made by mr. Friedman’, he said about SIGABA and SIGCUM:
‘We know now from Ticom reports that neither
the Japanese nor the Germans had the slightest success in their efforts to
solve messages in the Sigaba, though the Germans certainly tried hard enough.
The absolute security of Army and Navy high command and high echelon
communications throughout the war was made possible by the Sigaba’.
‘Results of Ticom operations have established
that neither the Germans nor the Japanese were successful in their efforts to
solve our Sigcum traffic, despite its great volume, and it is my belief that
had we used this machine for secret radio-teletype communications no serious
harm to our security would have followed’.
Was Friedman
correct? Were all high grade US cipher machines secure during the war?
Sunday, January 3, 2016
Unanswered questions of WWII cryptology – progress report
In January
2015 I wrote a summary of the progress I had made in researching some very
interesting cases of cryptologic history. What is the state of these cases now?
Let’s see.
1). US
State Department strip cipher
This case has
been (by far) the most difficult of those I’ve had to research. Despite this I
was able to make real progress in 2015. I located the report ‘JAT write up -
selections from JMA traffic' and used it to write an essay on the material
transmitted from Germany and Finland to Japan, I received the report I-89
‘Report
by Prof Dr. H Rohrbach of Pers Z S on American strip cipher’ and wrote
Compromise
of the State Department’s M-138-A strip cipher and the traffic of other US
agencies.
Also during
the year I managed to find a lot of material on the Finnish codebreakers and
their work on the M-138-A strip cipher. Regarding the Carlson-Goldsberry
report the NSA’s FOIA office has managed to locate it but releasing it will
take time.
2). NKVD
5th Department codebreakers
No new
information has been published on the work and achievements of the Soviet
codebreakers except for some online articles in Russian websites. The article ‘О ВКЛАДЕ СОВЕТСКИХ КРИПТОГРАФОВ В ПОБЕДУ ПОД МОСКВОЙ’,
referenced in the book ‘Near and Distant Neighbors: A New History of
Soviet Intelligence’, says
that in late 1942 the Soviet codebreakers analyzed the Enigma cipher
machine and developed ways of solving it. However their efforts failed in January 1943 due to German
security measures.
3). Referat
Vauck success
After
locating the reports of Referat 12 i was able to write the detailed essay Allied
agents codes and Referat 12. I’ve also requested the postwar interrogation
reports of Dr Wilhelm Vauck from the NSA. However locating and declassifying
them will take some time.
4). Forschungsamt
information
According to
the NSA’s FOIA office the Forschungsamt files are coming up for review.
5). German
Enigma investigations
The reports
of the German Army’s codebreakers on the Enigma are available from government
archives in the US and Germany. Unfortunately no one has read and commented on
them.
6). Japanese
Purple and Coral cipher machines
Regarding the
possibility of the Germans
solving the Japanese Purple cipher machine I haven’t found any new
information but in 2013 I had a
brief conversation with mr Otto Leiberich, who worked in the German cipher
department during the Cold War period. He told me that he had spoken with mr Cort
Rave about this case and he was able to give me some additional information.
I’ll write about this soon.
7). Soviet
diplomatic code
I’m satisfied
with the material
I’ve found but there is still the possibility that the Germans solved some
OTP traffic during WWII. Even if they did it is possible that the files were
destroyed during the war.
8). M-209
decoding device
In 2015 I
said ‘I have to say I’m still surprised
that this device has not received any attention from historians and/or the media!’ Since
then nothing has changed.
9). Unknown
unknowns
As Donald
Rumsfeld said ‘….. there are known
knowns; there are things we know we know. We also know there are known
unknowns; that is to say we know there are some things we do not know. But
there are also unknown unknowns – the ones we don't know we don't know…’.
Subscribe to:
Comments (Atom)